Synopsis
Introduction to basic concepts of computer security and demonstration of the main threats and challenges.
- Goal
- to be able to make informed choices in computer security and keep abreast of the major threats and best practices
Target
People comfortable with computers but without specialized knowledge of digital security issues.
Syllabus
- Presentation of the syllabus
- Distribution/handout to facilitate monitoring and for future reference
Definition
Question: What is security?
- Feeling versus fact
- National, personal, economic, food security
- Data, network, physical, etc.
Key Concepts
- There is no perfect security – security as a compromise (tradeoff)
- The weakest link – the security of a system
- Simple: safer and more reliable
- More expensive is not necessarily safer
- Security today, maybe not tomorrow – security as a process
Overview of computer network theory
- Client/Server
- Hop/Point to Point
- "IP" (address, routing)
- Global communication network
How to analyze a problem and its solution, 5 steps
- 5 steps
What assets should be protected?
Describe and understand what is at stake
what are the risks to these assets?
Consider what the possible attacks are, who would make them, why, etc.
To what extent has the problem been solved?
The problem is never completely resolved. look at how the solution interacts with the rest of the system and how it will fail
what are the new risks caused by the solution?
Consider the collateral damage or possible undesired consequences
What costs and compromises are imposed?
Every system has a cost and demand a compromise, social, economic, ecological, etc.
First described in Crypto-Gram Bruce Schneier in 2002 but better in his book "Beyond Fear" (2006)
Computer vulnerabilities
Workshop: what vulnerabilities are you aware of? how do you protect yourself? 2-3 cases, breakout sessions?
Social engineering - the human element
Things to protect
- Privacy - secrets!
- Anonymity - who you are
- Integrity - physical/image, destruction/deformation/defamation/identity theft
Privacy
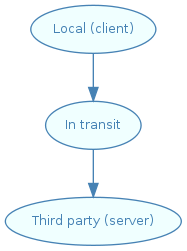
Locally stored information - theft or seizure
- Browser history of searches and page visits
- Cookies
- Documents (financial documents, personal letters, etc.)
- Locally stored email messages
- Computer viruses, worms, zombies
- Pirated software or media files
Information in transit
- Email messages (again)
- Phone (voip vs traditional)
- Banking
- Sites visited
- Documents exchanged
- Pirated software or media files, again
- Your location (cell, ipods, wifi)
- Firesheep
Information stored by a third party
- Facebook, gmail ... google!
Twitter (http://pleaserobme.com), flickr, blogs, google stalking ...
Foursquare, http://girlsaround.me/
- Voicemail
- Email (no IMAP/webmail, PGP, delete when read)
- IM (no Yahoo/MSN/IRC, logs kept at google, local logs)
- SMS (assume these are stored)
MyGoogle, iDrive, my cloud ...
- Search history
Physical safety
- Theft
- Webcams
- Microphones
- CDROMs, USB sticks
- Paper
- Access to machines
Intellectual Property/imaginary
- Authors
- Case of CD-ROMs which cannot be read in PS3 machines
- Companies
- General analysis of the case of DRM
- Example of iTunes movies
- Sony rootkit
- Kindle 1984
- What's at stake
- who controls culture?
Security server side
- DOS/demos (floods, crashes)
- Intrusions
- Disfigurements
- Data Theft
- Destruction
- Monitoring
- Theft of material/information
Practices
- Minimum privileges/"need to know"
- Trust: yes, up to a certain limit ("as necessary"?)
Web of trust - what does it do?
- Security culture and security practices
- Documenting and controlling physical access and keys
- Caretaker/maintenance staff? - who has access
- Keys? codes? - How we gain access
- Secure communications
- Managing passwords
Choose a good password http://xkcd.com/936/
- Write it in your wallet or store it as encrypted text
- Different passwords for different services (one per security level, or different everywhere)
- Password policies (not human readable, no defaults, carry them, password managers, different passwords, change passwords, not close to asset)
- Emails
- Do not click on emails that you do not want
- Do you really expect an attachment?
- Watch out for "phishing": your bank and paypal will never write to ask you to log in via a link
- Keep your machines up to date! Firewalls/antivirus
- Malware (no Microsoft, upgrade, and firewall tools, explain trojan vs virus vs worm)
- Retention and destruction of data (IM logs, secure deletion, destroy paper)
- Require passwords (screensavers, good passwords, passwords written down, guest accounts)
- Encrypt it
- Suggested systems
- Free software
- Mac vs Linux vs windows, the compromises
- Standard security software
- Place a poster of security practices in your office!
- Not to do:
- Install any old unsupported application
- Share passwords
- (Find examples of catastrophic security)
Questions
Feedback
- Do you feel more safe or less safe?
- Do you feel more capable of making decisions? Less capable?
Reference
Suggested Software
Multi-platform:
Libreoffice.org – office suite
Getfirefox.com - web browser
Getthunderbird.com - email client
Enigmail.mozdev.org - encryption for thunderbird
Gnupg.org - encryption command line
Jitsi.org - instant messaging, telephony and screen sharing secure
http://passwordmaker.org/ - browser password manager
Windows:
- Microsoft Security Essentials antivirus software
Linux:
- passwdqc - a good password generator
Other possible points
- Who would want to do this?
http://www.wired.com/threatlevel/2012/03/ff_nsadatacenter/all/1 / http://en.wikipedia.org/wiki/Utah_Data_Center - CIA/NSA
http://www.bbc.co.uk/news/world-middle-east-22287326 - Bashar al-Assad's Syrian Electronic Army
http://en.wikipedia.org/wiki/Operation_Aurora - computer security branch of the People's Liberation Army of China
https://en.wikipedia.org/wiki/PRISM_(surveillance_program) - the US government
http://www.cnn.com/2013/03/16/opinion/schneier-internet-surveillance - 100% complete security is impossible to achieve for individuals
Other documentation
https://pressfreedomfoundation.org/encryption-works - Encryption Works: How to Protect Your Privacy in the Age of NSA Surveillance
ssd.eff.org - This excellent site by the EFF is interesting, especially the tools section
Guide.boum.org - guide to computer security in French
https://help.riseup.net/security - email guide security
https://hatswitch.org/~nikita/courses/ece598nb-sp06/schedule.html - lots of reading
https://craphound.com/littlebrother/ and http://craphound.com/homeland/ - Novel by Cory Doctorow
http://privacysos.org/FAQ - anything to hide?
In this wiki:
 Le Wiki Koumbit
Le Wiki Koumbit